Simple
procedure analysis in search of anonymous and secure democratic
electronic
decision
making through Blockchain and Cryptocurrency accounting technology.
Can you trust
this?
Luis Rodriguez
mekhane@vmail.me
Introduction. Decentralization and accounting.
Electronic secret ballot voting is a subject long time expected since the very beginning of computer science. Making a simple automatic and anonymous process out of receiving and accounting votes is a promise that up to date the state of the art has not been able to accomplished for the majority of the population in some kind of anonymous way.
The method explained in this document does not solve the problem of trust within the voting community, thus it is not adequate for large groups of people not willing to be involved and motivated in the decision making process, making it more suitable for small and medium groups with clear goals and commitment, willing to participate in this experimental use of existing technology.
This document consists in a subjective analysis of how decentralized cryptocurrency blockchain technology could be used to the means of electronic vote counting, in order to deploy a relatively anonymous and secure election system. Concept hereby stated regards establishing a simple parallelism on value and votes accounting using such decentralized networks.
Cryptocurrency networks are designed to share and write a public transaction record file called Blockchain, along with intense cryptographic hashing power during its creation and consolidation.
Public and Private keys are created in order to access a specific amount in Cryptocurrency networks. These keys are unique and will not be generated again in our human time conception. Wallets allow you to create different addresses. If you are not familiar with Bitcoin technology and alternative cryptocoins, please take some time to find out more about this fascinating aspect of our emerging digital life.
Wallet as authorization token in identification process.
It is possible to use wallets from a chosen cyprocurrency in order to stablish a voting system. The wallet responsible for accounting votes can create different addresses that represent the options over which decision is considering. This information (address = option) is then sent to actual voters, each of them having a personal wallet and sufficient funds to participate. Voting will consist in making a prefixed transaction during a certain period of time into a predefined address, considering one transaction as one vote.
There are some requirements for the integrity of this method, most remarkable to be that every voter must be a trusted member of the community, and will only make the number and amount of transactions specified according to the consultation goal. Not following this procedure will invalidate the process. Wallet receiving and accounting transactions addresses must be newly generated for every new process, and must be kept only to the eyes of the voter during effective voting time.
One vote, one transaction. Simple Yes/No Referendum.
In this scenario we consider one administration wallet where payments = votes will be accounted, and different wallets (one wallet = one person / trusted operator) with n participants.
Wallet 1
→ generate address A (option = Yes)
→ generate address B (option = No)
→ generate address C (option = Blank)
Wallet n
→ send payment to chosen option = address
Each voter would choose from options and generate a transaction to one of the addresses previously created in the first wallet representing the available options. In a basic one person = one vote schema the most voted option would correspond to the address receiving the higher amount of currency according to public Blockchain public registry. Implementation could be easily scaled in order to fit more complex questions and possible outcomes.
Local implementation. Trusted operator.
This described method is valid for decentralized electronic decision making, but the voting process could be made locally by having a just one second wallet generating transactions and operated by a trusted third party, so called a trusted operator. This would allow the participation of any person that does not hold a cryptocurrency wallet and/or does not posses the required knowledge to operate it.
In this local scenario a unique sending address would easily allow individual option and user could not be linked, thereby granting anonymous voting right. However, matching local time stamps on single person physically accessing voting poll and transaction Blockchain timestamps could lead to a failure in the right for anonymity implementation.
A surface user friendly interface could be easily developed for this mean, making the potential voters not to have previous cryptocurrency knowledge use this technique, but it would have to be considered as a major critical security aspect.
General security considerations. Man and machine contact surface.
As public keys are inherently traceable in the Blockchain, voter identity could be obtained by linking user and wallet, as we all know. Voting wallets are to be kept private if considering the porpoise of anonymity. Accessing voting wallet could lead to current and previous options content data leak from user, even if different addresses have been issued in order to vote, showing transaction history.
Information linking actual options over consultation and addresses would be newly generated for each one of the consulting process, and it would be considered sensible information during voting and results accounting period of time, as any outside malicious non participant of the voting process could easily flood the consultation owning this suggested method.
This and more issues should be considered when willing to develop an end user interface towards this possibility of referendum, or in the event of writing simple applications to display results. Amount and number of transactions should be checked to fit number of participants. Participants must take part in voting process leaving no place for illegitimate votes.
Strong and anonymous? “No one can be trusted”.
We have seen how it is simple to achieve as much securitization and anonymity in voting as we have today available now in cryptocurrency, probably the strongest decentralized open source payment electronic mean operating in actual days, and along with the use of point to point encrypted connections over IPv6 new horizons are right now shaping the near future.
It is somehow possible to separate option and individual information in accounting process, thereby securing the transportation and publish accounting of votes, but the contact surface will always be susceptible of being compromised, just as it happens in cryptocurrency networks and in many aspects of human life.
If you are accessing your wallet in a compromised terminal there is no possible anonymous process. If a time stamp entry is being made on entrance over identification of voters on a local voting transactions could be matched to check blockchain time stamps, and many more real life security considerations that are only learned during implementation and testing activity.
New poll, new wallet. External attacks. “How to brick software” or “The Killswitch myth”.
A possible way to prevent data correlation techniques is to implement and generate a new wallet for every new poll. After process of voting access keys and wallet data are to be destroyed, buried, burned.
If poll accounting and/or voting wallet were to be compromised the transactions equivalent to votes could be obtained thus correlating option chosen by voter and poll. The best way not to leak any sensitive information is simply not holding it. It is strongly recommended that voter wallet is to be created new for each consultation process, and to be emptied and destroyed once consultation is over.
Killswitch myth stands for this game that would destroy itself once character died, and was not to be played ever again. In a similar way voting wallets could be bricked once voting period is over, and access information destroyed so there would be no holder of access key neither data files of used wallets.
Weak internal security. Trust in community. “All for one, one for all”
This simple voting method requires the trust of the voting community participating. Just as if you use cryptocurrency to pay in advance for a service you trust seller will deliver that service in agreed terms, participants in this process are required to be responsible for the whole process, having administrator rights to sabotage the poll just by voting twice. As we all know, great power comes with great responsibility.
Poll information should be propagated to users only by relatively secure means. Why not use TOR and a somehow point to point crypto secure email server? Voter is also responsible for keeping the information safe during voting time. It would be easy for a malicious external person to flood the poll just by knowing which addresses are related to the options in a running consulting process.
That is why voters must trust each other and have some kind of reputation, not for what they choose but for their correct participation in the deciding process. In example previously exposed only one vote per person is required, and any member that made double or no voting would inherently invalidate the consultation process.
This may look like something bad in first instance, buy may be a good way to oppose to a non agreed questions where all possible options considered are not included, and making so in the most anonymous possible way.
Right not to participate: Old school “machine without passwords”.
When trust is broken in a community of users there is no need to keep on trying. It is not a bug, it's a feature. If voting process is attacked from outside, it can be defended. But if it is sabotaged from inside, it is dangerous to keep on thinking that election holders are participating in a free voting process. So if one of the voters in the circle will not allow to hold clear elections -in the event of mismatching number of voters and number of transactions-, the whole process must to be radically reconsidered.
Demo 1: Simple question. Yes or No.
I am not aware at this moment of the state of the art regarding anonymous voting process platforms available. It has been an issue that has interested me for many years now, but that I never expected to see solved in a relatively simple way by using a technology designed for accounting coins into accounting votes. I cannot read code, so I have to trust that its open source nature makes it interesting for others to read it, and actually understand it, and hope that will make public considerations regarding what it runs on your machine. And ignorance is really not trusty. I do not trust code by default, so finding a way to vote with money and not needing a specific application made me even happier.
So we have certain requirements in order to easily create a democratic anonymous vote accounting process. First is what cryptocurrency we would like to choose. I decided to use Feathercoin because is cheap in these days, I have been able to mine a few coins with my pc, and I personally feel sympathy for this alternative coin. Any crypto you trust will do. Then we have to download a wallet, Feathercoin-qt on windows version for my example, and download the full Blockchain, thing that will take some time if you do for the first time.
Once we have our wallet software up and running we need to create a set of new addresses, one per option regarded in consultation question. This will generate a public address that will be use to vote. Each address and qr code will represent one of the possible outcomes of the consultation, and will demand a 1 FTC payment to voter supporting each option. Now we have everything ready to receive votes, and we have decided a certain period of time to “hold the elections”. Its the voters turn.
 Here we find all the information a responsible voter needs to accomplish his/her democratic duties. A *.zip file with instructions is to be sent using best possible mean. Vote fast, and hang the phone before machine identifies on going poll!
Here we find all the information a responsible voter needs to accomplish his/her democratic duties. A *.zip file with instructions is to be sent using best possible mean. Vote fast, and hang the phone before machine identifies on going poll!
Here I find two interesting operative alternatives. The first one allows to make electronic voting from the voter device as follows: Voter is to receive the information containing options and addresses related, makes the decision, and so proceeds to send payment to selected option. The second option is having a trusted wallet operator and setting a local voting place with enough privacy so to allow users scan the qr code with a mobile device wallet on site and all using the same terminal. In this event, authentication of voters in conventional would be needed, and privacy in voting action respected.
Feathercoin-qt wallet seems a nice option to use. Transaction details and voting account administrator panel as simple as it gets.
Public results displayed in different navigator windows. Real time and ready to grab, analyse and digest.
Android wallet sending funds representing vote.
Demo 2: Amnesic voting wallets: Bitcoin over Tails.
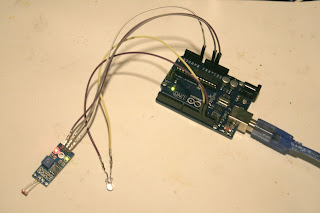
TAILS windows like live cd running on an old laptop with Electrum Bitcoin wallet pre-installed.
This procedure allows to create one disposable wallet to receive voting funds and thereafter participate in event. After sending vote to desired address = option, the wallet is somehow destroyed and user will keep no seed data information to recover. To this means Tails live distribution includes a Bitcoin Electrum pre-installed wallet, giving us the chance to test this particular method.
Payment sent to option desired. This is only to the eyes of the voter.
I send funds to this wallet -that will disappear once system is down, as far as I know- and also send relatively secure email with address to vote. In this particular example, due to the costs later on related, the decision making process will only be held by one person and there will be only one option. Freedom of choice granted!
Setting up three voting options in qr codes to be scanned: Cryptovoting poll ready.
It is possible to use this method both to make votes and to hold account of the votes. Wallets are to be destroyed once voting period is over, so the idea is to fund voting wallet, make voting with transactions to the poll holder wallet, empty the results accounting wallet (it would not be suitable to actually brick real value along with the information) recovering all funds minus commission charges. And there after, terminate wallets.
Big commission for small amounts. Not so nice.
Making transactions is charged with commission. In this particular case study 1 FTC transaction was charged with 0.01 FTC each making a total of 3 transactions. This is cheap. I had to make two Bitcoin transaction taking 0.0008 BTC and 0.002 BTC from qt wallet, and one from Android wallet charged with 0.0005. This is expensive. If you are going to try this at home I recommend you to use any alternative cryptocoin you trust. You need some hardware and software, and some humans in order to make it work.
Conclusions: Yes and/or No.
As mentioned before none of this does address the problem of trust within the voting community. But considering only anonymity aspect, it looks easy and relatively safe to implement a cheap voting system that would allow instant and vinculate decision making to any community willing to test the most similar thing to democracy I can think of. However, I personally do not know if using technology to vote is safe. I really would not use, unless you are already using another kind of system that you may not really trust to be secure and anonymous.
What was the question?
There is also a radical issue to consider: What is the question? Information access and specific knowledge about whatsoever issue is required, but also it is necessary to keep in mind the global aspect, the universal view. Wrong decision will be made if not having all the information, all points of view, or at least, the most.
In my opinion it is viable to make some experimentation in small or medium groups, with participants involved in the process of formulating questions and terms, decision responsibility taking and results implementation participation, all of this with a reasonable amount of privacy, at least for a while. All indications and procedures here stated are only for experimental use. If can use conventional means so to get voting, even better. Use at your own responsibility.
This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.
Gran Canaria, July 2015.
Download pdf file here